ECC Presentation - byu-ecc
advertisement

Elliptic Curve Cryptography
Implementation & PKI Adoption
Brian Saville
Jonathan Mitchell
Overview
•
•
•
•
•
•
•
Background of ECC and PKI
ECC Weaknesses
Experimentation
Results
ECC Adoption
Conclusion
Questions
Elliptic Curves
All Elliptic Curves come in the following form:
y2 = x3 + ax + b
Mathematical Properties
Can define a new algebra on
Elliptic Curves with interesting
mathematical properties:
• first, add a point-at-infinity O
• point addition: draw a line
through 2 points. the sum is the
opposite of where the line hits
the curve a 3rd time.
• adding point to itself: use
tangent line (point doubling)
• if vertical, sum is "O"
• this can also be determined
algebraically.
Point Addition: Rules
Finite Elliptic Curves
•
•
•
•
•
Encryption works better with integers.
Wrap elliptic curves in finite field (modulo)
Pretty curves and lines no longer applicable
Algebra still works
Curves now look like:
y2 mod p = (x3 +ax+b) mod p
Finite Point Addition: Rules
Uses in Cryptography
Mathematical properties are useful for PKI
• Can generate asymmetric (public/private) keys
• Can encrypt/decrypt data
Stronger than RSA
Key Generation
Agree on the following (public):
• Curve parameters (a, b)
• The modulus p
• Base point G (on the curve)
Pick a random integer n as private key
Calculate public key P = n*G
Encryption/Decryption
Alice represents her text or data to send as a point Pm
Alice sends Bob a pair of points:
SentPair = {k*G, Pm + k*P}
k = randomly chosen integer
Bob decrypts the message using his private key:
Pm + k*P - n(k*G) = Pm + k(n*G) - n(k*G) = Pm
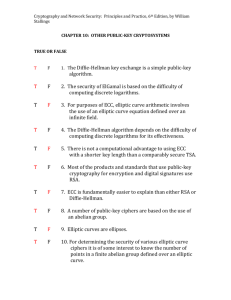
Why ECC is strong
The difficult mathematical problem is called the
elliptic curve discrete logarithm problem
That is, given P and G, (and P= n*G), find n
• Invented a whole new algebra
o not susceptible to common attacks
• Runs in exponential time
o RSA runs in sub-exponential time
• Best known attack: Pollard's rho attack (exponential)
o runs in ((πn)^1/2) / 2
Weaknesses
Unexplored since not used much in production
Choosing correct curve parameters
• Modulo p - some sub-exponential algorithms exist for certain
p
Finding base point G
• Not as easy as you'd think
Experiments - Goals and Outcomes
1. Create a visual representation of point addition
2. Perform timing experiments contrasting ECC and RSA
1.Length of time to generate keys (various key sizes)
2.Length of time to encrypt data (various data lengths)
Demo
Results
Key Generation by Key Size
Key Generation by Key Strength
Encryption by Key Size
Encryption by Key Strength
Analysis
Results are about as expected, with surprises
• Key generation was faster in ECC at same strength
• Encryption was faster in ECC at higher bit sizes
May have been due to naive implementation
ECC Adoption
Patents
• Many willing to work with community - Sun
• Certicom is the problem - Sued Sony
• NSA licensing from Certicom
Logistics
• Replace software and hardware in place for RSA, etc
Estimated standard ~2020
Conclusion
ECC is stronger than RSA for PKI
Patents won't stand in the way forever
Largest obstacle: replacing current PKI infrastructure
Review
• Background of ECC and PKI
o Elliptic Curves
o Key Generation
o Data Encryption
o Weaknesses
• Experimentation
o Visual Point Addition
o Key Generation
o Data Encryption
• Results
• ECC Adoption - Patents, Logistics
• Conclusion
Questions